You may have heard of the term ISO 27001 before but are not sure what significance it has for your company. You may also be considering implementing ISO 27001 for your new company and wants to find out how.
ISO 27001 is a security standard to safeguard companies’ assets and their customers’ data.
Recent news of data breaches has put the limelight on companies’ cybersecurity measures.
“More than 4,000 individuals’ medical data left exposed for 16 years” – 15 July 2022, The Daily Swig
“Razer sues IT vendor over data leak, says security breach caused US$7m in losses” – 13 July 2022, The Business Times
The consequences? Losses of millions of dollars and the reputation of an affected company is highly at stake.
Cybersecurity negligence in today’s data-driven world is something that any organization cannot afford to have especially when it comes to handling sensitive corporate information.
Implementing an effective information security management system (ISMS) protects yourself and your customers.
A system is a holistic approach for any organization in securing the confidentiality, integrity, and availability of corporate information assets.
In this article, we’ll look at how to implement ISO 27001 in ten easy steps.
What is ISO 27001 and why is it important
ISO/IEC 27001:2013 (also known as ISO 27001) is an internationally recognised standard for an information security management system (ISMS).
It is the latest version of the security standard published in 2013.
ISO 27001 is the leading standard focused on information security, published by the International Organization for Standardization (ISO), together with the International Electrotechnical Commission (IEC).

ISO 27001 standard provides a framework for any organization of any size to protect their information through implementing an ISMS.
This leading standard is very popular worldwide due to its international reputation.
According to IT Governance, a leading global provider of cyber risk and privacy management solutions, the number of ISO 27001 certifications has grown by more than a whooping 450% in the past decade.
It is important to be ISO 27001 certified so that you can gain the confidence and trust of relevant stakeholders and customers. It shows them that your organization is serious about information security.
What does it mean to be ISO 27001 certified
Being certified with a respectable standard demonstrates to your existing and potential customers or clients that you have built an ISMS capable of data protection.
An ISMS comprises of:
– hardware and software used for information security,
– rules on how you use, store and retrieve information
– how you assess and mitigate information security risks and
– how you improve information security continuously
To be certified, your ISMS needs to be audited and assessed to see if it meets the requirements of the standard.

Benefits of ISO 27001 certification
1. Gain credibility
Retention of existing customers is higher while new customers or clients are more likely to come to you too as you gain credibility from the certification.
You may also win over clients or customers who used to be hesitant to purchase from you or work with you.
The return on investment (ROI) from an effective ISMS can be high and hence more attractive especially when you have an ISO 27001 ISMS that stakeholders can trust.
2. Improve company culture
As ISO 27001 involves people not just processes and technology, your staff will be involved and challenged to embrace information security as part of their working ethics.
Your employees will feel they are contributing to something important and of value.
SVM Cards Europe was quoted in a British Standards Institution (BSI)’s case study:
“Taking a standards-based approach to information security has changed the way we work as an organization, supporting our business growth whilst allowing us to keep our core values.” Cordelia Maden, Talent Manager CVM Europe
3. Increase cyber resilience
An ISO 27001 ISMS requires your organization to be adaptable to the highly evolving cyber landscape and make constant adjustments to your security measures.
So, are you ready to kickstart your successful ISO story?
Read on to find out.
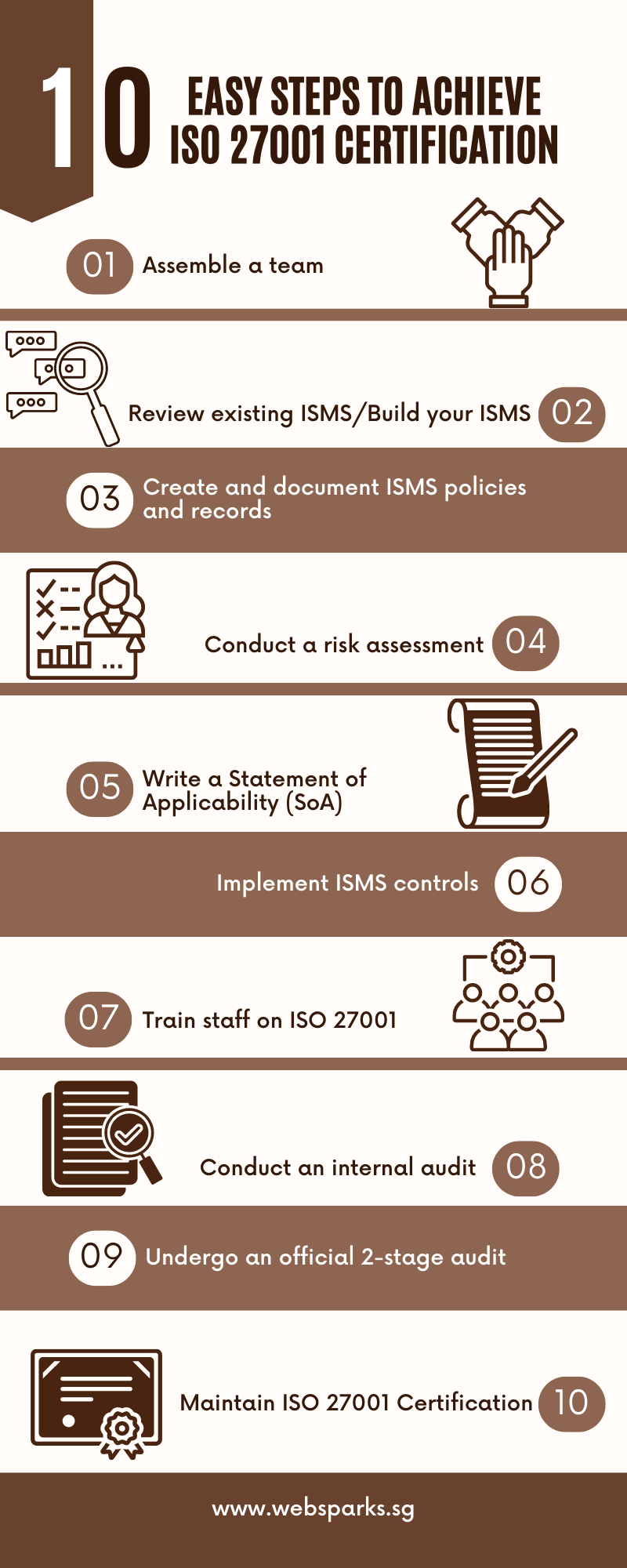
10 easy steps to ISO 27001 certification
While this checklist serves as a good guide, the process may be different for every organization.
The differences can be due to your existing information security management system (ISMS), organizational size, and existing documentation.
Step 1: Assemble a team
- Assign a project leader with strong knowledge of information technology, familiarity with the organization’s processes, and good communication skills to lead a team
- Establish roles and responsibilities within the team
Step 2: Review existing ISMS or build your ISMS
- Understand the requirements of the standard
- Identify gaps in the existing ISMS documentation
- Determine the scope of implementation concerning your company business: e.g., the entire company to be covered and what type of service(s) to be covered?
- Set project goals, duration or timeline, costs, and type of management support needed after you have identified the gaps.
Step 3: Create and document ISMS policies and records
- Create a process-based approach for your ISMS where you can continually make updates and improvements
- Document ISO 27001 policies and procedures using ISO 27001 templates
- Finalise and publish records and documents
Step 4: Conduct a risk assessment
- Use a risk matrix to identify, evaluate and measure areas of risk to data security
- Create a response plan for each identified risk
- Assign team members to follow up on necessary actions
Step 5: Write a Statement of Applicability (SoA)
- Be familiar with the 114 controls of Annex A of the ISO 27001 guidelines
- Select the controls that best address your identified risks in your risk assessment
- Create a Statement of Applicability (SoA) that includes the selected ISO 27001 controls and the actions taken to address those identified risks
Step 6: Implement ISMS controls
- Share the policies and inform staff of the new procedures
- Update software and make changes according to the new controls
- Monitor and review ISMS for improvements needed
Step 7: Train staff on ISO 27001
- Conduct regular training to drive security awareness among the staff
- Educate staff on new terms in ISO 27001 and the importance of being certified
- Highlight the implications of failing to comply with security requirements
Step 8: Conduct an internal audit
- After all the documentation and implementation of ISO 27001, this is the time to test your new controls and systems
- Choose an objective auditor that is not involved in the ISMS team to conduct the audit
- Record and make necessary changes before the official audit
Step 9: Undergo an official 2-stage audit
- Look for an accredited ISO 27001 auditor from a recognized accreditation body
- The process involves documentation review in Stage 1 and site tests on your ISMS in Stage 2
- After all the major nonconformities have been addressed, you’ll be ISO 27001 certified
Step 10: Maintain ISO 27001 Certification
- An ISO 27001 certification lasts for three years.
- During this time, your organization still needs to conduct risk assessments and surveillance audits each year
- Conduct management reviews annually on your ISMS and conduct ongoing staff training
- Prepare for the renewal audit in the third year by updating your policies and documents
In conclusion, start by building up an ISMS that aligns with the requirements of ISO 27001.
Conduct regular reviews and audits of your system to ensure the best protection is provided for your company.
Being certified ensures trust in your information security systems and helps minimise risks of potential cybersecurity attacks in the long run.
Websparks is an ISO 27001-certified company
Websparks is an ISO 27001-certified web solutions company in Singapore.
We are also ISO 9001-certified and award-winning where we meet and exceed clients’ expectations with the services we provide.
Check out our available services.
Schedule a consultation with us on how we can meet your digital needs today.